As you probably know the DEP (Data Execution Prevention) was introduced in XPSP2 and it prevents code to be executed from data sections.
Let’s consider this code snippet:
[cc lang=”cpp”]unsigned char b = 0xC3; // ret
int _tmain(int argc, _TCHAR* argv[])
{
void *addr = &b;
__asm call addr;
getchar();
return 0;
}[/cc]
This code sample will crash if the DEP is enabled. DEP is a very important security improvement against buffer overlow exploits, but it might be generate incompatibility with older applications which rely on executing code inside the data section.
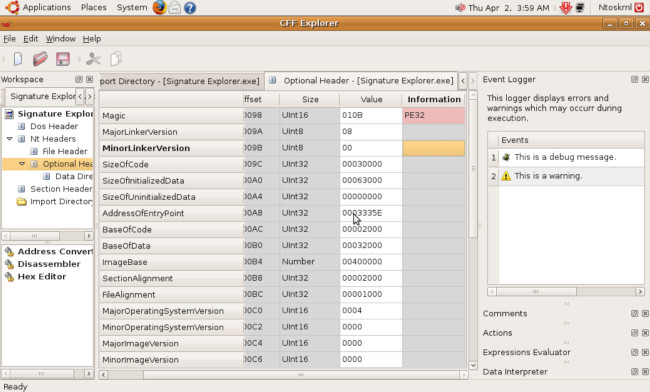
The DEP can be disabled individually for an executable. The only thing which needs to be done is to unset the “NX Compatibility” flag inside “Optional Header -> Characteristics”.
Make sure to have the latest CFF Explorer release. I also updated the flags of the “Characteristics” field, because they were outdated. Among the new flags there is the ASLR flag (DLL can move), which enables the executable to be relocated at a random (256 possibilities) address if it contains a relocation table.
Both the ASLR and the DEP flag are enabled by default in Visual C++.
Another flag is the “Code Integrity” one. This flag when set checks the digital signature of the executable and runs it only if the signature is correct.